Burp Suite is an essential tool for web application security testing, available in community, professional, and enterprise editions. This guide provides an examination of Burp Suite’s features, best practices, installation methods on various operating systems, and a detailed case study demonstrating its application in addressing modern cybersecurity threats. You will learn how to use Burp Suite to prevent data breaches through systematic vulnerability assessment and exploitation testing.
The rapid expansion of web applications has increased the attack surface for cyber threats. As a cybersecurity professional, tools like Burp Suite are indispensable in ensuring the integrity, confidentiality, and availability of web applications. Burp Suite integrates various functionalities necessary for the thorough assessment and exploitation of web application vulnerabilities.
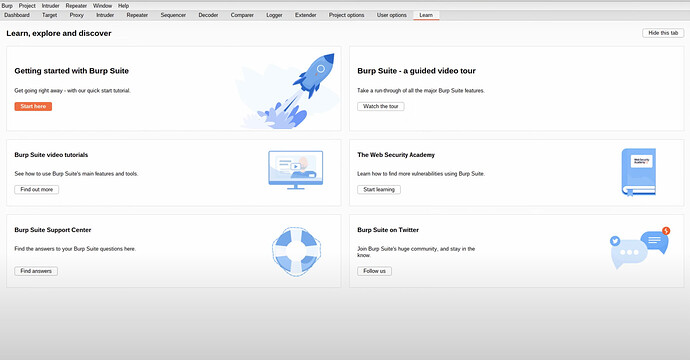
Key Features of Burp Suite
Burp Suite offers a robust platform for web application security testing, encompassing a suite of tools designed for detailed analysis and exploitation:
-
Proxy: Facilitates the interception and modification of HTTP/S traffic between the browser and web servers, allowing for detailed analysis and manipulation of requests and responses.
-
Spider: Automates the crawling of web applications to map content and functionality, uncovering all accessible endpoints.
-
Scanner: Conducts automated vulnerability scans to identify common security flaws in web applications, including SQL injection, XSS, and more.
-
Intruder: Enables automated customized attacks, providing a powerful tool for brute-forcing and parameter fuzzing.
-
Repeater: Allows manual modification and re-sending of individual HTTP requests for detailed testing and analysis.
-
Sequencer: Analyzes the randomness of session tokens to identify potential weaknesses in session management.
-
Decoder: Converts encoded data into readable formats and vice versa, facilitating the analysis of encoded information.
-
Comparer: Performs data comparison to identify differences between two sets of information, useful for spotting subtle changes.
-
Extender: Extends Burp Suite’s functionality through BApp extensions, allowing for custom enhancements and integration with other tools.
Installation Guide for Burp Suite
Windows
To install Burp Suite on Windows, download the installer from the PortSwigger website. Execute the installer and follow the on-screen instructions to complete the installation. Once installed, launch Burp Suite from the Start menu or desktop shortcut.
Linux
For Linux, specifically Kali Linux where Burp Suite is often pre-installed, additional installation can be performed using the following steps.
Download the installer from the PortSwigger website, make the installer executable with chmod +x burpsuite_community_v1.7.36.sh, and execute it with ./burpsuite_community_v1.7.36.sh. Follow the installation prompts to complete the setup.
macOS
On macOS, download the installer from the PortSwigger website. Open the downloaded .dmg file, drag the Burp Suite icon to the Applications folder, and launch Burp Suite from the Applications folder or Launchpad.
Configuring Burp Suite on Kali Linux
Burp Suite is typically pre-installed on Kali Linux. To verify or install, use the command:
sudo apt-get install burpsuite
After installation, configure your browser to route traffic through Burp’s proxy by setting the proxy settings to 127.0.0.1:8080. Import Burp’s CA certificate into the browser to intercept HTTPS traffic without SSL warnings.
Example: Preventing a SQL Injection Attack
In this section, you will learn how to use Burp Suite to detect and prevent a SQL injection attack on a web application. This example assumes that you have already configured Burp Suite as described in the previous sections.
Step 1: Proxy Setup and Interception
Objective: Intercept and analyze HTTP/S traffic to identify potentially vulnerable parameters.
- Launch Burp Suite: Open Burp Suite on your Kali Linux machine.
- Navigate to the Proxy Tab: Ensure that the “Intercept is on” button is enabled.
- Configure Your Browser: Set your browser’s proxy settings to route traffic through Burp Suite (typically 127.0.0.1:8080).
- Visit the Target Web Application: Open your browser and navigate to the target web application.
- Intercept Traffic: Burp Suite will start intercepting HTTP/S traffic. Look for HTTP requests containing parameters in the URL or body that could be susceptible to SQL injection.
- Send Requests to Other Tools: For any interesting request, right-click on it and send it to the Repeater, Scanner, or Intruder for further analysis.
Best Practice: Organize your workflow by labelling and commenting on intercepted requests within Burp Suite to keep track of potential vulnerabilities.
Step 2: Spidering the Application
Objective: Automatically crawl the web application to discover all content and potential endpoints.
- Go to the Target Tab: Select the site map of the target application.
- Initiate Spidering: Right-click on the target application and choose “Spider this host”.
- Configure Spider Settings: Set the spidering configuration to include authenticated areas if you have credentials. This helps in identifying all possible endpoints.
- Monitor Spidering Progress: Keep an eye on the spider’s progress and adjust settings as necessary to ensure thorough coverage.
Best Practice: Combine manual browsing with spidering to ensure that dynamically generated content, such as JavaScript-based endpoints, is also discovered.
Step 3: Scanning for Vulnerabilities
Objective: Use Burp’s Scanner to automatically detect vulnerabilities, including SQL injection points.
- Select the Target: In the site map, right-click on the target application and select “Scan”.
- Configure the Scan: Customize the scan settings to focus on SQL injection. You can adjust the scan’s speed, depth, and coverage.
- Initiate the Scan: Start the scan and let Burp Suite analyze the web application for vulnerabilities.
- Review Scan Results: Once the scan is complete, review the identified issues, particularly any SQL injection vulnerabilities.
Best Practice: Schedule scans during off-peak hours to avoid impacting the performance of production environments.
Step 4: Manual Testing with Intruder
Objective: Use Burp’s Intruder tool to perform automated, customized attacks to confirm the presence of SQL injection vulnerabilities.
- Send Request to Intruder: From the Proxy or Target tab, identify a request with parameters and right-click to send it to Intruder.
- Configure Positions: Mark the parameters in the request where you suspect SQL injection might be possible.
- Set Payloads: Choose payloads such as
' OR 1=1 --to test for SQL injection. - Start the Attack: Run the Intruder attack and analyze the responses for indications of successful injection, such as changes in the response body, status codes, or server errors.
Best Practice: Use payload lists tailored for SQL injection and include a mix of common and uncommon payloads to cover various injection vectors.
Step 5: Exploiting with Repeater
Objective: Manually verify and exploit SQL injection vulnerabilities using Burp’s Repeater tool.
- Send Request to Repeater: Identify the vulnerable request from Intruder or Proxy and send it to Repeater.
- Craft SQL Injection Payloads: Manually modify the parameter values to inject SQL commands. Start with simple payloads like
' OR 1=1 --and gradually increase complexity. - Send and Analyze Requests: Send the modified requests and carefully analyze the server’s responses for evidence of successful exploitation. Look for returned data, errors, or changes in the application behaviour.
- Extract Data: If the injection is successful, craft payloads to extract data, such as
' UNION SELECT username, password FROM users --.
Best Practice: Take detailed notes and screenshots of each step and result, which will be useful for reporting and further analysis.
Step 6: Mitigation Strategies
Objective: Provide actionable recommendations to the development team to fix identified vulnerabilities.
- Report Findings: Compile a detailed report of the findings, including the vulnerable parameters, payloads used, and evidence of exploitation.
- Recommend Security Measures: Advise the development team to use prepared statements and parameterized queries to prevent SQL injection. Emphasize the importance of input validation and sanitization.
- Suggest Regular Audits: Recommend regular security audits and the implementation of automated testing to catch vulnerabilities early.
Best Practice: Collaborate with the development team to implement fixes and validate the remediation by re-testing the application.
Advanced Features
Advanced users can enhance Burp Suite’s functionality through extensions available in the BApp Store. Automating workflows for repetitive tasks can improve efficiency. Customizing scan settings allows for more comprehensive security testing. For advanced scenarios, such as detecting out-of-band vulnerabilities, utilize Burp Collaborator.
Burp Suite is an essential tool for web application security testing, providing a comprehensive suite of features for identifying and mitigating vulnerabilities. By adhering to best practices and leveraging Burp Suite’s advanced capabilities on Kali Linux, cybersecurity professionals can prevent data breaches and enhance the security posture of web applications.